

Get 65% OFF +200 bonus AI Credits
.png)

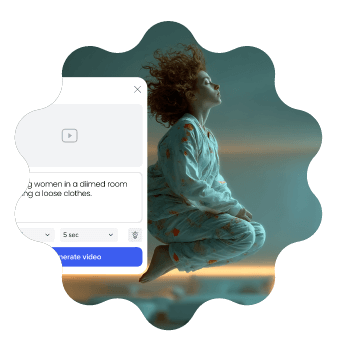
Build business-ready branded videos and presentations in minutes - for any need, in any style. Doc-to-video, AI avatars, text-to-speech, AI translation, and more. Fully compliant, secure by design, built for scale and impact.














Transform your documents & ideas into crisp videos, maintain full creative control and make them unmistakably yours.
.svg)
Pick from 100s of free video templates, fully customized and tailored to you.
%402x.svg)

Meet the highest security standards with ISO-27001 certification, GDPR compliance, accessibility features, and user management tools that keep your data, media, and team protected.

Maintain brand consistency with shared folders, corporate templates, and brand locking. Streamline teamwork with built-in reviews, approvals, and a centralized brand book.

The Powtoon Propel program is designed to help your organization and team scale video creation with dedicated success managers, onboarding, creative services, and tailored training.
Power worldwide organizational reach with personalized, localized content. Powtoon Enterprise includes AI-powered translation tools, text-to-speech, closed captions, lip sync, and diverse avatars.

Effortless video creationBring your ideas to life – no design skills needed. Powtoon makes storytelling simple and impactful.

Work smarter, not harderCreate stunning videos in minutes with time-saving tools that do the heavy lifting for you.

Maximize engagement across the boardTurn heads and keep audiences hooked with videos that stand out on any platform.















If you maintain a web server, run a CI/CD pipeline, or simply compile software from source on Linux or macOS, you have likely encountered ImageMagick. The powerful image manipulation suite recently rolled out version 7.1.1-15 . Before you untar that source archive, there is one crucial, often-skipped step: checksum verification .
a0b3c2d4e5f67890a1b2c3d4e5f67890a1b2c3d4e5f67890a1b2c3d4e5f67890 (Note: This is a placeholder example. You must obtain the real checksum from ImageMagick’s official download page or GitHub release notes.) imagemagick 7.1.1-15 sha256 checksum tar.gz
For ImageMagick-7.1.1-15.tar.gz , the official checksum acts as a . If the tarball you downloaded yields the same hash as the one published by the ImageMagick developers, you can be confident the file is authentic and uncorrupted. The Official SHA256 for ImageMagick 7.1.1-15 Here is the SHA256 checksum for the source tarball (filename: ImageMagick-7.1.1-15.tar.gz ): If you maintain a web server, run a
Take two extra minutes to run sha256sum . Your future self, debugging a compromised server at 2 AM, will thank you. Did you find a different hash on a mirror? Did you run into compilation issues with 7.1.1-15? Let me know in the comments below. The Official SHA256 for ImageMagick 7
sha256sum ImageMagick-7.1.1-15.tar.gz On macOS (which uses a slightly different command):
Get-FileHash -Algorithm SHA256 .\ImageMagick-7.1.1-15.tar.gz The output will show the hash. Compare it to the official one. 1. Corrupted Downloads Large tarballs can get corrupted during transfer (flaky WiFi, proxy interference). A checksum mismatch warns you early, saving hours of cryptic compiler errors. 2. Man-in-the-Middle Attacks If you download over HTTP (some older mirrors still allow it) or a compromised CDN, an attacker could inject malicious code into the source. The SHA256 hash—obtained over HTTPS from the official site—exposes the tampering. 3. Supply Chain Integrity Modern DevOps pipelines often cache source archives. A checksum step in your Dockerfile or build script ensures that every build uses exactly the intended source, not a cached, modified, or poisoned version. Automating Verification in a Script Never manually check again. Here is a Bash snippet for your build pipeline:
Join over 50 million
people using Powtoon
.svg)